Purpose Beyond Profit
In working with Teneo, you are helping to improve the lives of a million children around the world. Learn more
In working with Teneo, you are helping to improve the lives of a million children around the world. Learn more
Most Network and Security teams are overworked so making progress is a challenge. We securely connect users to their applications by combining leading technology with expert guidance. You stay in control, simplify your operations and keep ahead of the game.
Over 22 years, we’ve helped hundreds of successful global Enterprise Network & Security leaders through transformation. Join them and experience the difference:
Network and security teams often face an overload of tasks, managing complex systems that are costly and difficult to maintain, especially when key experts leave. These complexities can lead to insecure and inefficient business operations. Simplifying these systems reduces risks, saves money, and improves efficiency and user experience.
Teneo specializes in simplifying technology through innovation. We assess your current setup and goals, offer fresh ideas, and provide strong implementation and ongoing support. Our mission is to “open minds to new possibilities”, ensuring easier and secure application access for users. Ultimately, connecting users in a way that is secure and optimized and observable will allow your team to deliver what the business needs.
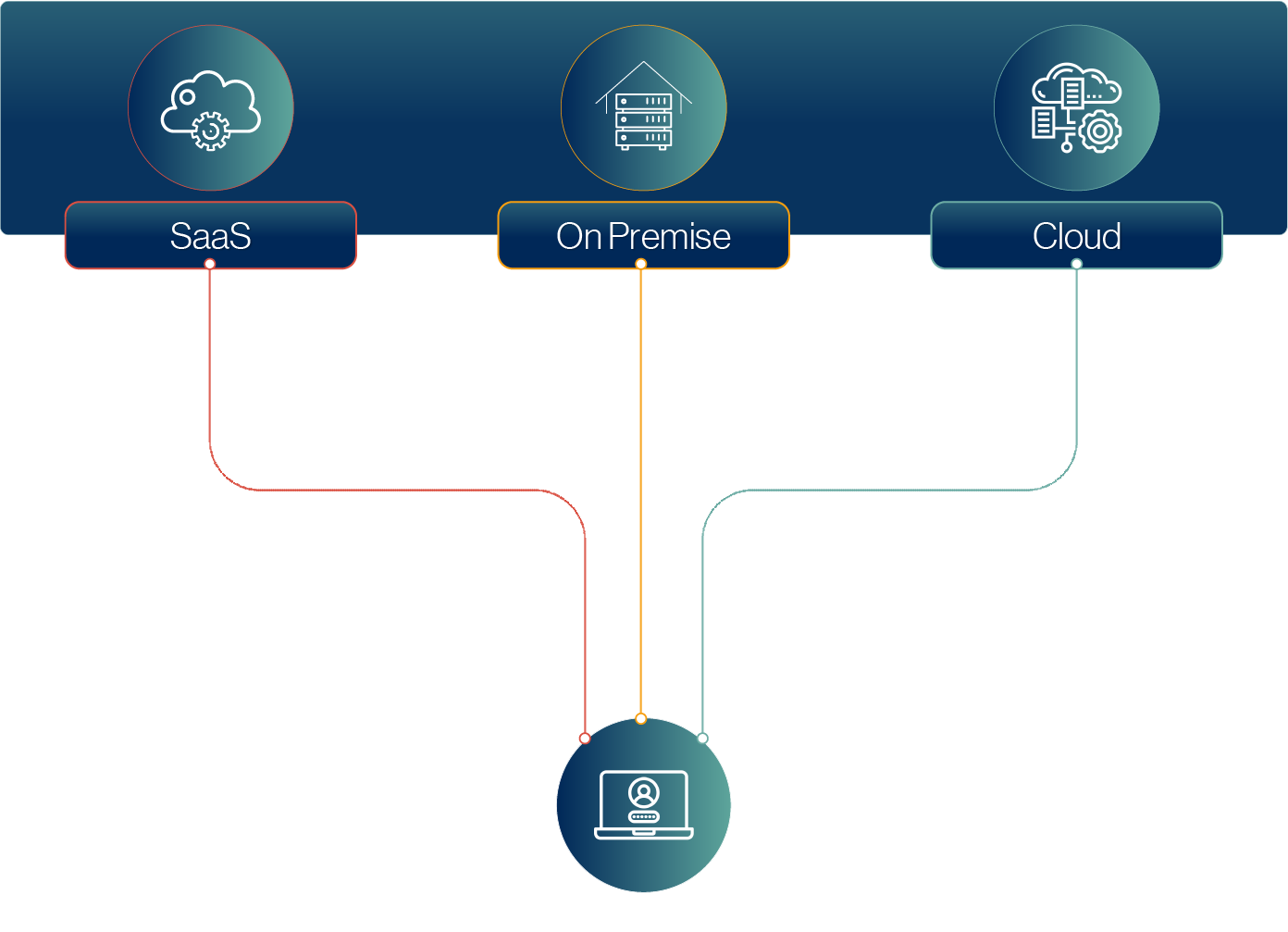
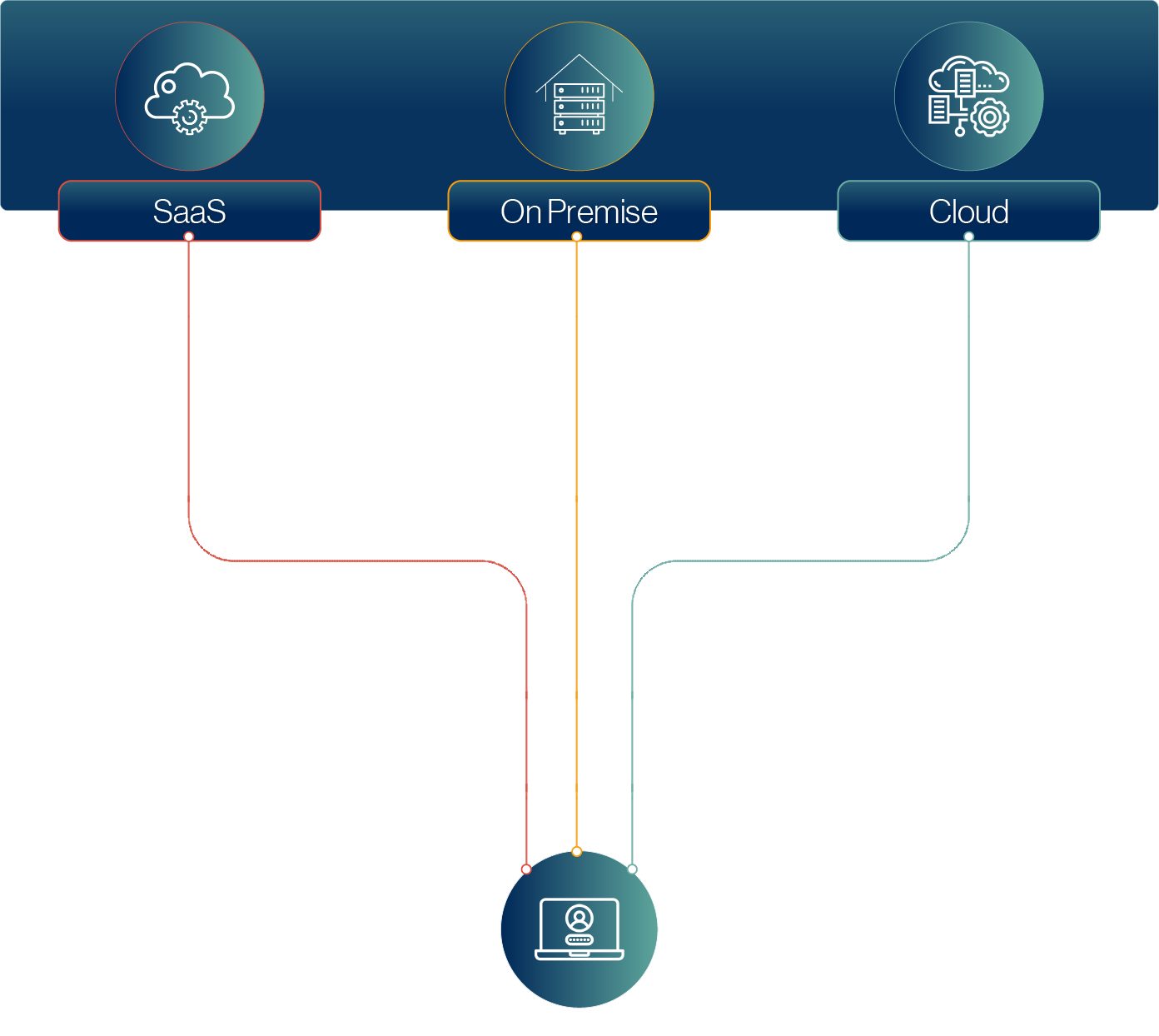
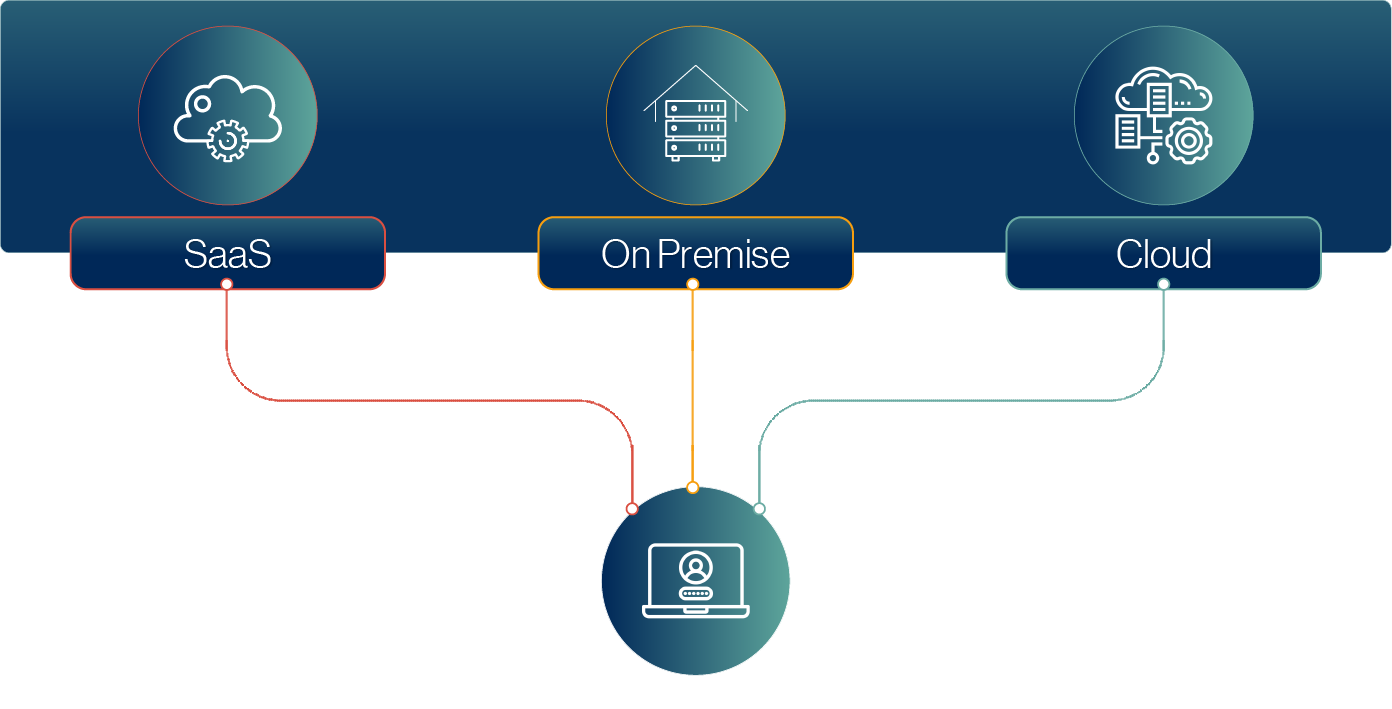
To help businesses achieve this, we created StreamlineX, an innovative framework combining market-leading technologies.
The Teneo StreamlineX framework brings together eight key areas critical to modern IT infrastructure, which encompass AI Network Operations to Advanced End Point Protection. The roadmap of innovation we develop with you might include simplifying network and security in a SASE model, using AI to optimize end user security or shining a light on your users’ experience to gain the insights needed to make changes where it matters most.
Teneo’s business growth is spurred on by a passion for helping others. We know that the bigger we are, the more we can give back. That’s why we’ve pledged to donate 1% of revenue to help improve the lives of 1 million children around the world. Find out more about our purpose.





Let us know when you’re available to talk. You can tell us about your priorities and help us to understand your needs.
You’ll feel reassured as we help you to build an agile roadmap that reaches your goals. We’ll validate your ideas, align resources and help you with any unknown unknowns.
Get started on your transformation journey with an initial professional services engagement that lets you experience our expertise for extra peace of mind.
See how our IT services set you up for success, and embrace innovation with confidence!
You stay in control, simplify your operations and keep ahead of the game.

This website uses cookies so we can provide you with the best user experience possible.
Cookies are small files containing information that enables a website to recognise you. They’re downloaded to the device you use when you visit a website and sent back to that website each time you re-visit, or sent to another website that recognises the same cookie.
Our cookie policy tells you how and why we use cookies, and how this allows us to improve your online experience. You can read our full Cookie Policy here.
Strictly necessary cookies include session cookies and persistent cookies. Session cookies keep track of your current visit and how you navigate the site. They only last for the duration of your visit and are deleted from your device when you close your Internet browser. Persistent cookies last after you’ve closed your Internet browser and enable our website to recognise you as a repeat visitor and remember your actions and preferences when you return.
Third party cookies include performance cookies and targeting cookies. Performance cookies collect information about how you use a website, e.g. which pages you go to most often, and if you get error messages from web pages. These cookies don’t collect information that identifies you personally as a visitor, although they might collect the IP address of the device you use to access the site. Targeting cookies collect information about your browsing habits. They are usually placed by advertising networks such as Google. The cookies remember that you have visited a website and this information is shared with other organisations such as media publishers.
Keeping these cookies enabled helps us to improve our website and display content that is more relevant to you and your interests across the Google content network.
Please enable Strictly Necessary Cookies first so that we can save your preferences!
Whenever you give us your personal data, you must consent to its collection and use in accordance with our privacy policy. This includes our use of cookies. You can read our full Privacy Policy here.